Cybersecurity researchers have took the wraps off an on-going cyber fraud operation led by hackers in Gaza, West Bank, and Egypt to compromise VoIP servers of more than 1,200 organizations across 60 countries over the past 12 months.
According to findings published by Check Point Research, the threat actors — believed to be located in the Palestinian Gaza Strip — have targeted Sangoma PBX, an open-sourced user interface that's used to manage and control Asterisk VoIP phone systems, particularly the Session Initiation Protocol (SIP) servers.
"Hacking SIP servers and gaining control allows hackers to abuse them in several ways," the cybersecurity firm noted in its analysis. "One of the more complex and interesting ways is abusing the servers to make outgoing phone calls, which are also used to generate profits. Making calls is a legitimate feature, therefore it's hard to detect when a server has been exploited."
By selling phone numbers, call plans, and live access to compromised VoIP services from targeted businesses to the highest bidders, the operators of the campaign have generated hundreds of thousands of dollars in profit, alongside equipping them with capabilities to eavesdrop on legitimate calls.
Exploiting a Remote Admin Authentication Bypass Flaw.
PBX, short for private branch exchange is a switching system that's used to establish and control telephone calls between telecommunication endpoints, such as customary telephone sets, destinations on the public switched telephone network (PSTN), and devices or services on voice over Internet Protocol (VoIP) networks.
Check Point's research found that the attack exploits CVE-2019-19006 (CVSS score 9.8), a critical vulnerability impacting the administrator web interface of FreePBX and PBXact, potentially allowing unauthorized users to gain admin access to the system by sending specially crafted packets to the affected server.
The remote admin authentication bypass flaw affects FreePBX versions 15.0.16.26 and below, 14.0.13.11 and below, and 13.0.197.13 and below and was patched by Sangoma in November 2019.
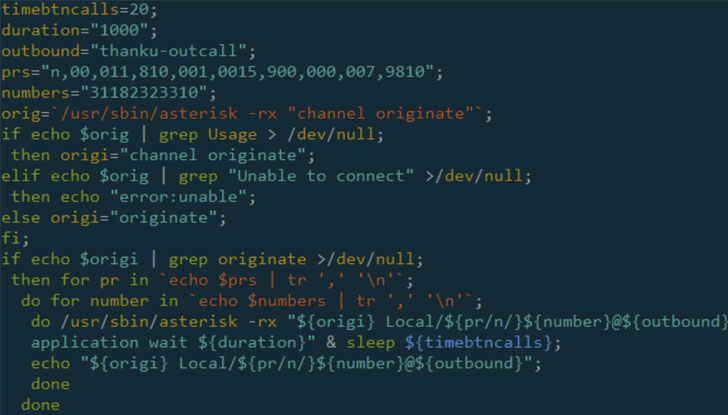
"The attack begins with SIPVicious, a popular tool suite for auditing SIP-based VoIP systems," the researchers noted. "The attacker uses the 'svmapmodule' to scan the internet for SIP systems running vulnerable FreePBX versions. Once found, the attacker exploits CVE-2019-19006, gaining admin access to the system."
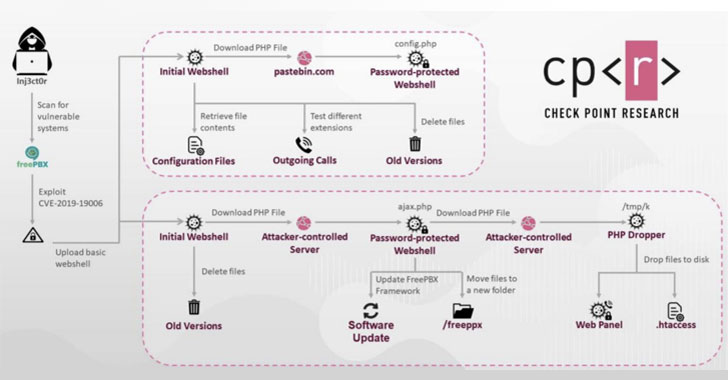
In one attack flow, it was discovered that an initial PHP web shell was used to get hold of the FreePBX system's database and passwords for different SIP extensions, granting the attackers unrestricted access to the entire system and the ability to make calls out of every extension.
In the second version of the attack, the initial web shell was utilized to download a base64-encoded PHP file, which is then decoded to launch a web panel that lets the adversary place calls using the compromised system with both FreePBX and Elastix support, as well as run arbitrary and hard-coded commands.
The campaign's reliance on Pastebin to download password-protected web shells has tied the attack to an uploader by the name of "INJ3CTOR3," whose name is linked to an old SIP Remote Code Execution vulnerability (CVE-2014-7235) in addition to a number of private Facebook groups that are used to share SIP server exploits.
A Case of International Revenue Share Fraud
Check Point researchers posited that the hacked VoIP servers could be employed by the attackers to make calls to International Premium Rate Numbers (IPRN) under their control. IPRNs are specialized numbers used by businesses to offer phone-based purchases and other services — like putting callers on hold — for a higher fee.
This fee is typically passed on to customers who make the calls to these premium numbers, making it a system ripe for abuse. Thus, the more calls the owner of an IPRN receives and the longer clients wait in the line to complete the transaction, the more money it can charge telecom providers and customers.
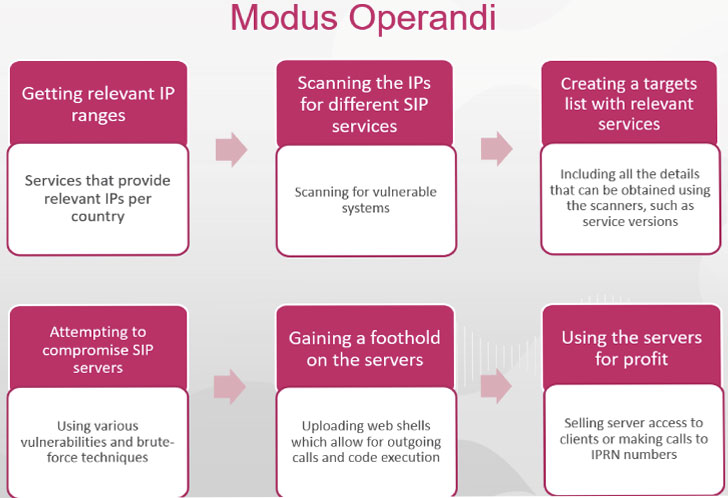
"Using IPRN programs not only allows the hacker to make calls but also abuse the SIP servers to generate profits," the researchers said. "The more servers exploited, the more calls to the IPRN can be made."
This is not the first time switching systems have been exploited for International Revenue Share Fraud (IRSF) — the practice of illegally gaining access to an operator's network in order to inflate traffic to phone numbers obtained from an IPRN provider.
Back in September, ESET researchers uncovered Linux malware dubbed "CDRThief" that targets VoIP softswitches in an attempt to steal phone call metadata and carry out IRSF schemes.
"Our research reveals how hackers in Gaza and the West Bank are making their money, given the dire socio-economic conditions in the Palestinian territories," said Adi Ikan, head of network cybersecurity research at Check Point.
"Their cyber fraud operation is a quick way to make large sums of money, fast. More broadly, we're seeing a widespread phenomenon of hackers using social media to scale the hacking and monetization of VoIP systems this year."
"The attack on Asterisk servers is also unusual in that the threat actors' goal is to not only sell access to compromised systems, but also use the systems' infrastructure to generate profit. The concept of IPRN allows a direct link between making phone calls and making money."
THN
#hashtags
#osutayusuf
Comments
Post a Comment